I am currently working on a Cloud migragion project. The goal is to move the on-premise applications (mostly are Atlassian tools) to AWS. And we need to build everything from scratch. I take it as a good opportunity to refresh what I learned in the past a few years, and also implement the best practices that I have summarized.
First thing first, you should always start with securing your AWS login. Read the IAM best practices if you have not. What I normally do is to finish the initial setup (billing, contacts info…), turn on CloudTrail, then lock away root account with MFA enabled. Setup SAML federation and let users to use SSO to login.
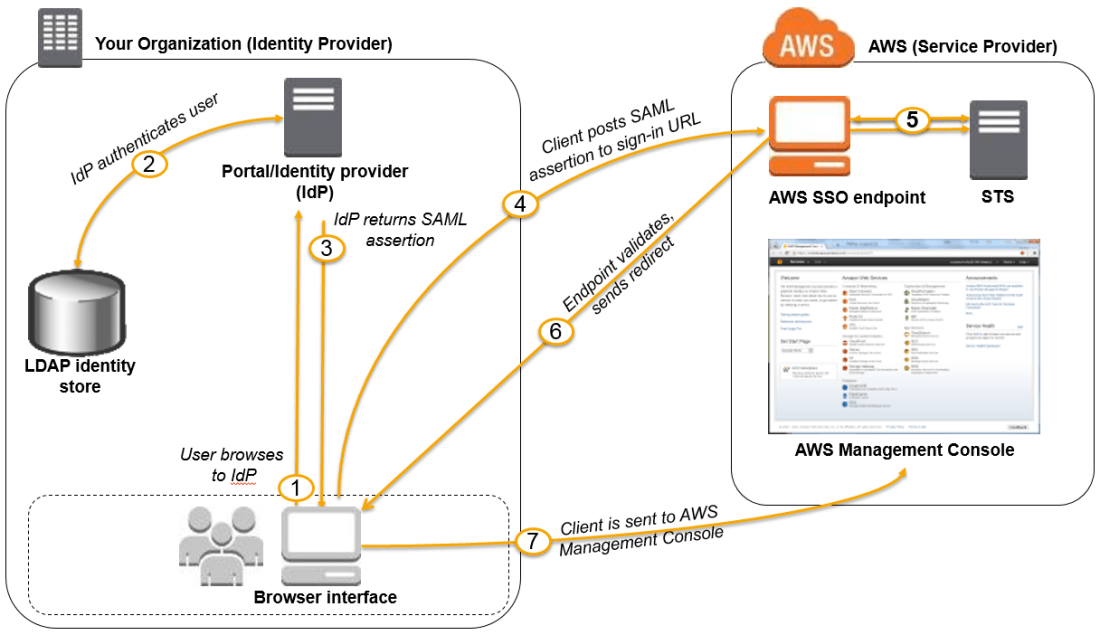
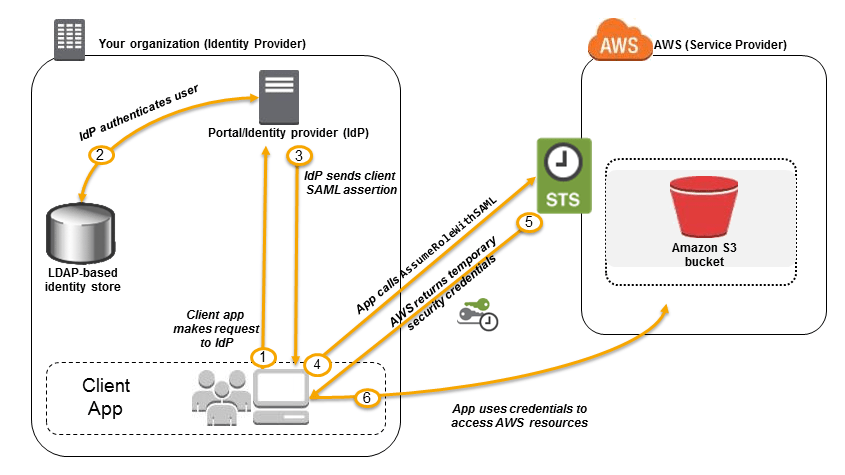
There are two types of access to AWS: Console and API. The SSO login process works in similar way. There are two parts in SAML based federation: IDP (Identity provider) and SP (Service Provider). Here are the simple steps to set it up:
- Register SP (which is AWS in this case) with your IDP (popular providers) by using AWS saml metadata file.
- Register IDP within your AWS account IAM by using your IDP saml metadata file.
- Create roles in AWS, and assign permissions policies accordinly.
- Create groups in your organization directory (normally it is LDAP based), and add associated users into the group.
- Configure SAML assertion for authentication, this will link the group/user to the right roles.
Two nice diagrams that I found on AWS site: