We use Cloud Conformity as a compliance check tool against our AWS environments. Recently, there is a new check failed – ELBv2 ALB Security Group, and the given reason is Load Balancer [alb-d-LoadB-XXXXXXXX] is not associated with valid and secure security groups.
I have confirmed that the ALB is associated with a valid and security group, as it exactly matches AWS Recommended rules.

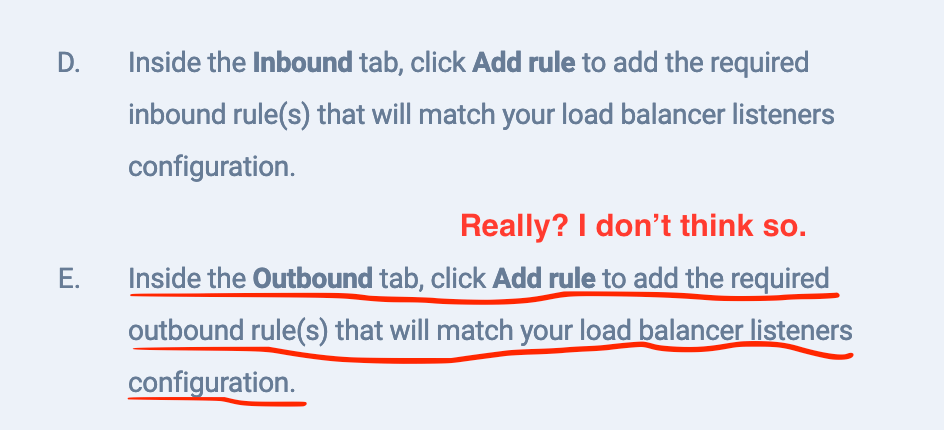
By reading Cloud Conformity ELBv2 ALB Security Group KB, I am 100% sure this is a BUG in this rule. According to what is written as below, they think the ELB security group outbound port should the same as the inbound port. Really? I don’t think so. As a typical scenario, the http SSL traffics terminate at ALB (e.g listener is 443), and the traffics between ALB and EC2 are http (e.g EC2 listener is 80).
I have raised a bug report with them. Any updates will be posted here.
Update – 30/07/2020
Cloud Confirmity has confirmed this BUG, and will fix it.
Reply from Cloud Conformity
Thank you for investigating rule ELBv2-006 thoroughly. We have discussed your input, and agree there are changes required to correct the implementation around the outbound logic. Thank you for your patience, and our apologies for any inconvenience. We recommend that you disable this rule in the mean-time until we introduce the proposed changes.