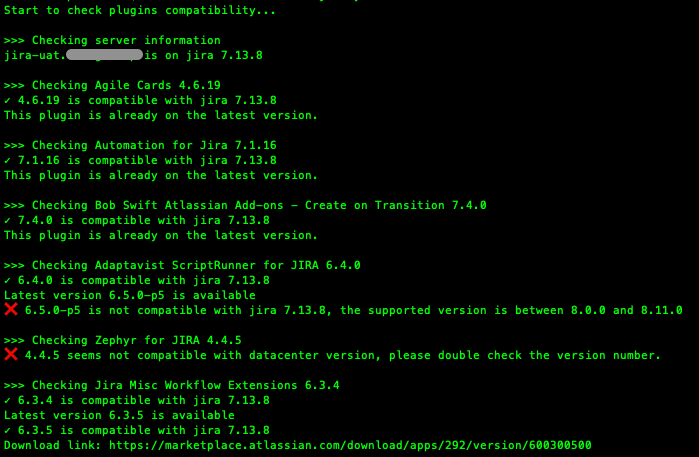
What a beautiful sunny morning! I started my day with 9KM run, then followed by cold shower and a cup of hot coffee. Feel great! 🤘🏽OK, lets get down to business 🙂 I got a new idea for my next open source project (also my August challenge). It is to automate Atlassian add-on management. Just … Continue reading Automate Atlassian Add-on Management Part One
Author: Jackie Chen
AWS Security Checklist
Identity & Access Management Secure AWS account (AWS organization, MFA).Rely on centralized identity provider (SSO).Use multiple AWS accounts ot separate workloads and workloads stages such as production and non-production (SCP, Guardrails, Control Tower).Store and use secret securely (STS, Secrets Manager). Detection Enable foundation security services (AWS CloudTrail, Amazon GuardDuty, and AWS Security Hub).Configure service and … Continue reading AWS Security Checklist
ELBv2 ALB Security Group Check in Cloud Conformity
We use Cloud Conformity as a compliance check tool against our AWS environments. Recently, there is a new check failed - ELBv2 ALB Security Group, and the given reason is Load Balancer [alb-d-LoadB-XXXXXXXX] is not associated with valid and secure security groups. I have confirmed that the ALB is associated with a valid and security … Continue reading ELBv2 ALB Security Group Check in Cloud Conformity
Access Specific EC2 behind ALB
When there are multiple EC2 instances running behind the application load balancer, there is no way (at least as the time of writing) to tell the load balancer which instance you want to use. It is all controlled by the pre-defined load_balancing.algorithm.type. load_balancing.algorithm.type - The load balancing algorithm determines how the load balancer selects targets when routing … Continue reading Access Specific EC2 behind ALB
Service Role for CodeBuild
Do you notice anything that is not right in the following CloudFormation template? ... Resources: CodeBuildServiceRole: # IAM role for the codebuild project. Type: AWS::IAM::Role Properties: RoleName: !Sub ${ProjectName}-CodeBuild-ServiceRole Path: /team-abc/ AssumeRolePolicyDocument: Version: "2012-10-17" Statement: - Action: ['sts:AssumeRole'] Effect: Allow Principal: Service: ['codebuild.amazonaws.com'] Policies: - PolicyName: !Sub ${ProjectName}-CodeBuild-Policy PolicyDocument: Version: "2012-10-17" Statement: - Action: # … Continue reading Service Role for CodeBuild