Question: Using the credentials for one IAM role 1 to assume a different IAM role 2, what is the maximum duration of the new credentials?
A. Same as Role 1
B. Same as Role 2
C. Same as the role (1 or 2) which has longer maximum duration
D. Same as the role (1 or 2) which has shorter maximum duration
E. 15 minutes
F. 1 hour
Scroll down to see answer 🙂
Answer: F
Role chaining
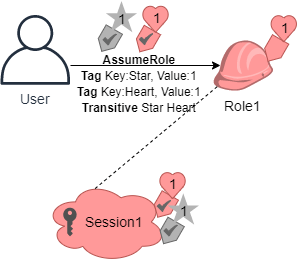
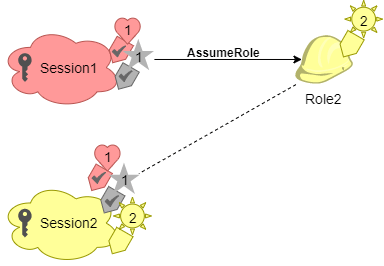
Role chaining occurs when you use a role to assume a second role through the AWS CLI or API. For example, assume that User1 has permission to assume RoleA and RoleB. Additionally, RoleA has permission to assume RoleB. You can assume RoleA by using User1‘s long-term user credentials in the AssumeRole API operation. This operation returns RoleA short-term credentials. To engage in role chaining, you can use RoleA‘s short-term credentials to assume RoleB.
When you assume a role, you can pass a session tag and set the tag as transitive. Transitive session tags are passed to all subsequent sessions in a role chain. To learn more about session tags, see Passing Session Tags in AWS STS.
Role chaining limits your AWS CLI or AWS API role session to a maximum of one hour. When you use the AssumeRole API operation to assume a role, you can specify the duration of your role session with the DurationSeconds parameter. You can specify a parameter value of up to 43200 seconds (12 hours), depending on the maximum session duration setting for your role. However, if you assume a role using role chaining and provide a DurationSeconds parameter value greater than one hour, the operation fails.
AWS does not treat using roles to grant permissions to applications that run on EC2 instances as role chaining.
Reference: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_use.html