Simply speaking ACM (AWS Certificate Manager) uses KMS (Key Management Service) to protects the private key. What drew my attention into this topic is that a user get denied (no permission to describe kms key) when trying to request a ACM certificate in a region where KMS is explicitly denied.
This diagrams explains how ACM use KMS:
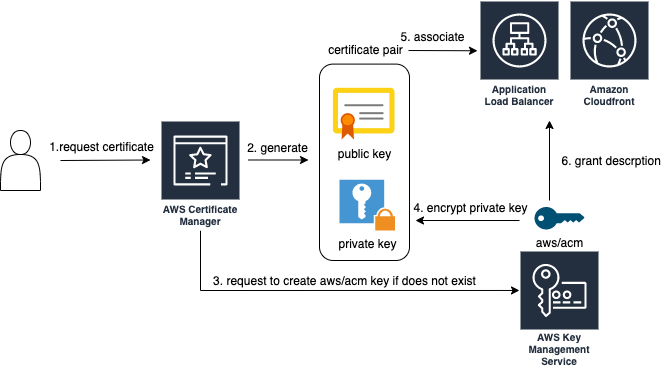
- User requests a certificate in ACM.
- ACM generates a public/private key pair. ACM stores the certificate and its corresponding private key.
- If the key aws/acm (alias) does not exist in KMS, ACM creates an CMK in KMS with the alias aws/acm. This CMK is unique in each AWS account and each AWS Region.
- ACM uses the aws/acm key to encrypt the private key and only stores the encrypted version.
- User associates the certificate with a AWS service that is integrated with ACM, e.g ELB, CloudFront.
- A grant is automatically created to allow the AWS service to use the aws/acm key to decrypt the private key. The integrated the AWS service use the decrypted private key and the public key to establish the secured the connections with clients. When the certificate is disassociated from the integrated service, the grant is retired.
It is typical that one AWS service requires another AWS service to work, e.g AWS backup uses S3 for storage, ACM uses KMS to encrypt and decrypt the private key. So when design the permissions, we have to keep that in mind.
Reference: https://docs.aws.amazon.com/acm/latest/userguide/data-protection.html