AWS SSM Session Manager is a great addition to the existing AWS services, simply speaking it provides a secured, manageable and easier way to access the instance inside the VPC, and more (e.g. port forwarding).
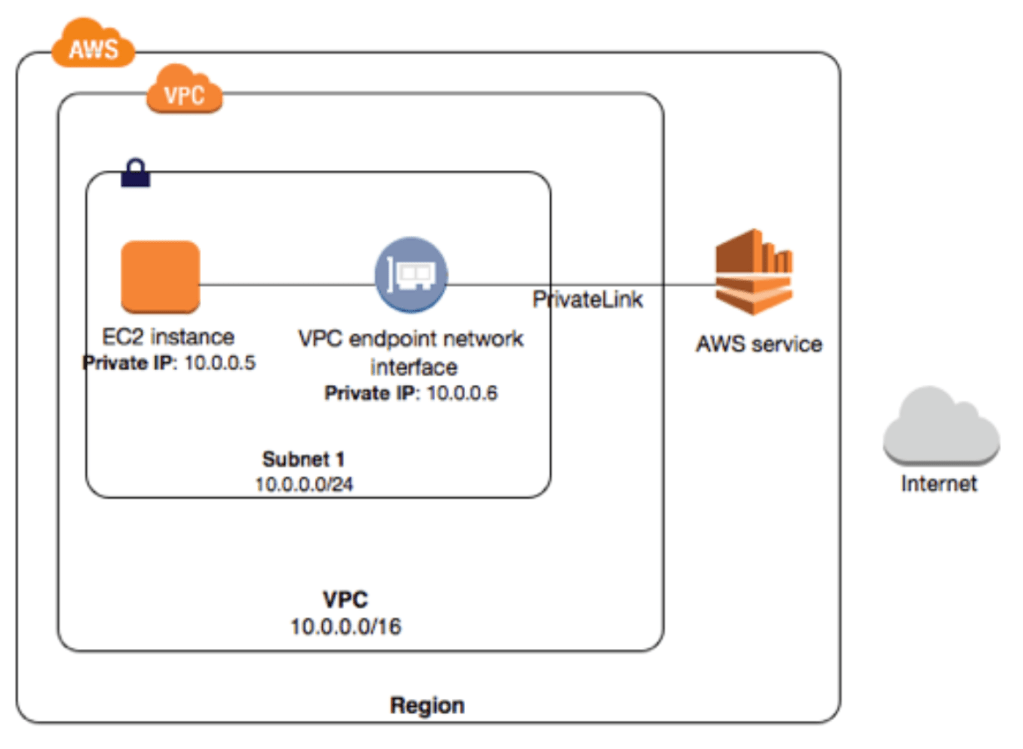
There are two ways to use session manager: over Internet vs over PrivateLink.
- Over Internet: The instance communicates to the public SSM endpoint that is open on the Internet.
- Over PrivateLink: The instance communicate to the private SSM endpoint which is exposed to the VPC where the instance is hosted.
Personally I prefer to use it over the PrivateLink which offers a higher security standard. But of course nothing comes free, it has extra cost for the endpoint and its associated traffics. This is how the topology looks like:
Here is the How-To steps:
First of all, you have to have the ssm-agent running in your instance. If the instance use Amazon AMI, the newer version should already have it installed by default. Refer working with SSM agent for details if needed. In my example, I use the latest Amazon Linux 2 AMI which comes with ssm-agent. If your instance does not have it, please refer how to manually install ssm-agent.
Once the instance ready to go. You need to create an instance profile and attach to the instance. This allows the EC2 instance to use SSM service and also upload the logs (like session history) to a S3 bucket.
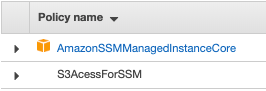
AmazonSSMManagedInstanceCore is AWS managed policy. S3AccessForSSM is an inline policy. Replace <region> and <bucket-name> with your ones.
Next, create the following four endpoints for your VPC.
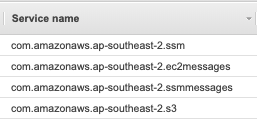
For com.amazonaws.ap-southeast-2.ssm, com.amazonaws.ap-southeast-2.ec2messages, com.amazonaws.ap-southeast-2.ssmmessages, choose the same subnets as the instances as it needs to create a network interface in the subnet for the private link. The security group should allow the instances to access TCP 443 (just use the security group that the instances are associated as the source).
For com.amazonaws.ap-southeast-2.s3, choose the same route table as your instance subnets, it will automatically add a new route entry.
By now, you should be able to use the session manager over the PrivateLink! Either use the console (under SSM) or aws cli (aws ssm start-session –target <instance-id>)
To use aws cli to launch session manager, the Session Manager Plugin has to be installed on your machine.
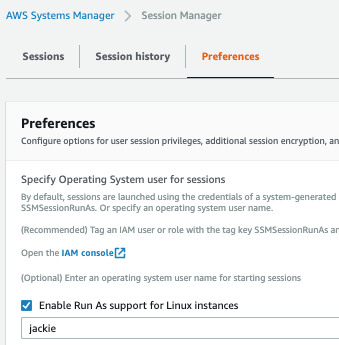
By default, the login user is ssm-user with sudo privilege. If you would like to login as a different use, then you need to:
Firstly, create a user inside the instance
# Sample – add user named Jackie
useradd jackie
echo ‘jackie ALL=(ALL) NOPASSWD:ALL’ > /etc/sudoers.d/jackie
chmod 440 /etc/sudoers.d/jackie
Secondly, configure the RunAs user in the Session Manager Console. Optionally, you can configure the Bucket where you want to save the logs (should be same as the <bucket-name> that is in the S3AccessForSSM policy. Also you can turn on the encryption for better security.
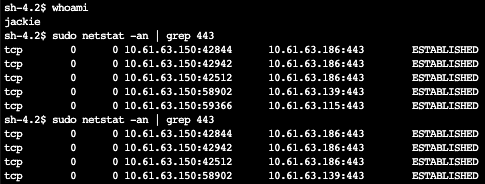
Here we go, here is my aws cli remote session over the PrivateLink.
l99730770:~ jchen$ aws ssm start-session –target i-0ed6e403138xxxxxx
Starting session with SessionId: jchen-05cb43157e0404dc6
sh-4.2$
sh-4.2$ whoami
jackie
sh-4.2$ netstat -an | grep 443
tcp 0 0 10.61.63.150:42844 10.61.63.186:443 ESTABLISHED
tcp 0 0 10.61.63.150:50964 10.61.63.113:443 ESTABLISHED
tcp 0 1 10.61.63.150:40184 52.119.211.230:443 SYN_SENT
tcp 0 0 10.61.63.150:42512 10.61.63.186:443 ESTABLISHED
tcp 0 0 10.61.63.150:58524 10.61.63.172:443 ESTABLISHED
Session Manager builds a tunnel over websocket, so only https is needed, no more 22 and ssh key are required.
This is the Web console remote session. Isn’t it cool?
References:
https://aws.amazon.com/premiumsupport/knowledge-center/ec2-systems-manager-vpc-endpoints/
One thought on “Use AWS SSM Session Manager Over PrivateLink”