AWS Trusted Advisor recently added a new check ‘Exposed Access Key’ in Security category. This to checks popular code repositories for access keys that have been exposed to the public and for irregular Amazon Elastic Compute Cloud (Amazon EC2) usage that could be the result of a compromised access key.
By default Trusted Advisor run checks every 24 hours. For such critical check, we probably want to run it more frequent, say every 30 minutes. Currently, AWS trusted advisor does not support custom schedule. Per the conversation I had with the AWS support, they are working on event trigger notification feature for Trusted Advisor.
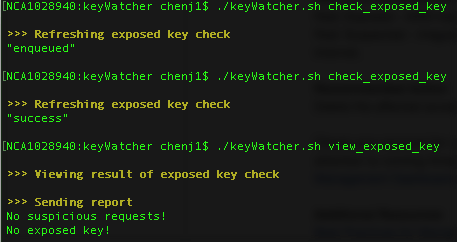
While waiting that feature becomes available. I have added this feature into AWS keyWatcher v0.3, and create a cronjob to let it run every 30 minutes.
Here is how it works: